You're most likely here because you are an IT administrator and you have a network that deploys Windows Updates via Windows Server Update Services or WSUS. Perhaps you're relatively new to WSUS or you're a veteran that has been using the product since its inception. In either case, you are mostly frustrated because even in the latest release of WSUS that there is no reliable way to force clients to check in and report their status. You know about wuauclt /reportnow and /detectnow. You may even be aware of the .NET method (New-Object -ComObject Microsoft.Update.AutoUpdate).DetectNow().
But despite having tried everything, you're at at a loss. All you want is for your clients to report their current status into WSUS on demand. Is that really too much to ask? Actually, it might be. If you google "force wsus client to check in to wsus server", you'll see almost 300,000 results. And I swear I've read every single one of them and tried every single suggestion.
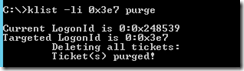
I finally decided to take matters into my own hands. I built a lab environment consisting of a domain controller, a WSUS server and a client machine. I then proceeded to deep dive with process monitor and packet analyzers to try and find a way to "trick" the WSUS client into thinking it's time to report in. After many hours at this, I was just about to give up when I accidentally stumbled upon the magic command I was looking for.